Cybersecurity for Direct Primary Care
Your Patients Trust You With Their Health. Trust Us With Their Data.
You can't see patients until you're HIPAA compliant. Tuearis Cyber builds and runs the program that gets you there. HITRUST-tested, deployed in days, and built to scale from first patient to full growth.
The only vendor in our client's entire technology stack that required zero modifications to pass HITRUST certification.
From 20 employees to 1,500. One partner, zero service disruptions

Built for Healthcare Startups
If Your Organization Just Received Funding and Needs a Security Program That Can Keep Up, This Is for You.
Direct Primary Care is one of the fastest-growing models in U.S. healthcare. Recent regulatory changes have made DPC membership fees more tax-efficient, more employer-friendly, and more attractive to investors than ever before, which means more practices launching, more funding flowing in, and more pressure to achieve HIPAA compliance quickly.
Here is the challenge: most funded DPC practices have a compelling care model, a talented founding team, and almost no cybersecurity infrastructure. You cannot build a practice on a foundation that leaves patient data exposed. Your investors know that. Your board knows that. Your future payers know that.
Qualifier checklist
- You recently received funding (seed, Series A, or grant)
- You are pre-revenue or early-revenue and patients are coming soon
- You do not have an internal security team yet
- Your CIO or CTO was just hired or you are still conducting that search
- You know you need HIPAA compliance but are not sure where to start
- You are evaluating vendors who lead with tools rather than outcomes
If that describes your organization

tuearis cyber
Over 175,000 devices secured from thousands of threats, every day.
With over 15 years of cybersecurity experience, Tuearis Cyber (pronounced “two-are-is”), and derived from Latin, meaning “guardian” is the most trusted managed security services provider for mid-market organizations in high-risk industries.
We pride ourselves on being an extension of your existing team and deliver comprehensive, custom security services using only the best in cybersecurity technology.
The Stakes
A PHI Breach Before You See Your First Patient Is Not Just a Fine. It Is a Threat to Everything You Have Built
For a funded DPC practice, a cybersecurity failure is not an inconvenience. The consequences compound quickly and they do not stay contained

You cannot operate
Ransomware can take your systems offline for days, sometimes weeks. No systems means no patients. No patients means no revenue. No revenue means no practice

Your investors take notice
Boards treat security failures as leadership failures. Funding rounds get withheld. Founders get removed. It does not matter how much you built or how long it took. If the board holds fiduciary responsibility and a preventable breach occurred on your watch, you are accountable

You become publicly listed
A confirmed breach triggers mandatory reporting to the HHS Breach Portal, publicly searchable and permanently on record, widely referred to in the industry as the "Wall of Shame." Affected patients must be notified. Payer contracts can be suspended or terminated. Future funding partners will find the listing before they return your cal

The regulatory penalties are substantial
OCR violations carry fines ranging from tens of thousands to millions of dollars per violation per year, accompanied by multi-year corrective action plans and sustained oversight that extends well beyond the breach itself

Your cyber insurance position deteriorates
Premiums increase. Coverage limits shrink. Exclusions are added. Future insurers require full breach disclosure. You cannot conceal it and you cannot recover from it quietly
The organizations that get this wrong rarely make the mistake of underinvesting twice. The CTO who approved the lower-cost vendor, the CFO who deferred the budget, the CEO who believed it could wait: we have seen the consequences play out firsthand. Do not allow "we will address security after we reach our growth targets" to become the most consequential decision your practice ever makes.
tuearis cyber
Best-In-Class,
Year-Over-Year
We don’t just claim we’re good at what we do, we show it, through our work and our recognitions.

Best in Managed Security Services - USA
Corporate America Today Annual Awards 2022

Best in Managed Security Solutions
Innovation and Excellence Awards 2022 and 2021 Corporate LiveWire

Most Promising Enterprise Security Solutions Provider 2023
CIO Top 20 Enterprise Security Providers 2023

Best Managed Cybersecurity Provider - USA
2020 and 2021 Software and Technology Awards - New World Report
What We Do
We Build Your
HIPAA-Compliant Security Program. You Focus on Patient Care
Tuearis Cyber does not sell you a collection of tools and call it a program. We design, deploy, and operate a complete HIPAA-compliant cybersecurity program validated in live HITRUST audits.
Our standard program covers every major HIPAA security requirement: continuous threat monitoring, endpoint detection and response, email security, vulnerability management, device controls, and incident response. All of it is included in your managed service with no surprise billing.
You get a direct line to our team, not a ticketing queue. Executive dashboards show exactly what is covered and how your program is performing, without requiring you to interpret technical reports. And a flat, predictable billing model means your team will never hesitate to reach out.
DPC practices are built on direct, trust-based relationships between providers and patients. We believe your security partner should operate the same way.

HIPAA Compliance, Built In
Our program is structured from day one around HIPAA's technical safeguard requirements so that when your audit arrives, nothing needs to change.

Visibility Without Complexity
Executive dashboards present your coverage status clearly. No acronyms, no lengthy technical reports. Just direct answers to the question your leadership team is actually asking: are we covered?

Deployed in Days, Not Months
We are active in your environment within 10 days of contract execution. We can advise on security events even before full deployment is complete.
Why Organizations Trust Us
A partner, Not Just a Provider
You don’t need another vendor, you need a cybersecurity partner who understands your industry, your infrastructure, and your limitations. Tuearis works as an extension of your team, delivering solutions that are practical, fast to deploy, and easy to operationalize. Whether you’re under audit, responding to an incident, or proactively improving controls, we’re here to simplify and strengthen your security posture.


A Program, Not a Product Stack
Most security vendors deliver tools. You are left to determine how they integrate, where the gaps remain, and how to articulate your compliance posture to a regulator. We take a different approach.
Every Tuearis engagement begins with one question: what does your HIPAA program actually require? From there, we map our services to your specific obligations across administrative safeguards, technical safeguards, breach notification requirements, and documentation standards. We tell you precisely what we cover, what your organization owns internally, and where the line falls.
When you are a managed security client, incident response on protected devices is included. No unexpected invoices. No urgency in finding an outside forensics team at 2am. We already know your environment.
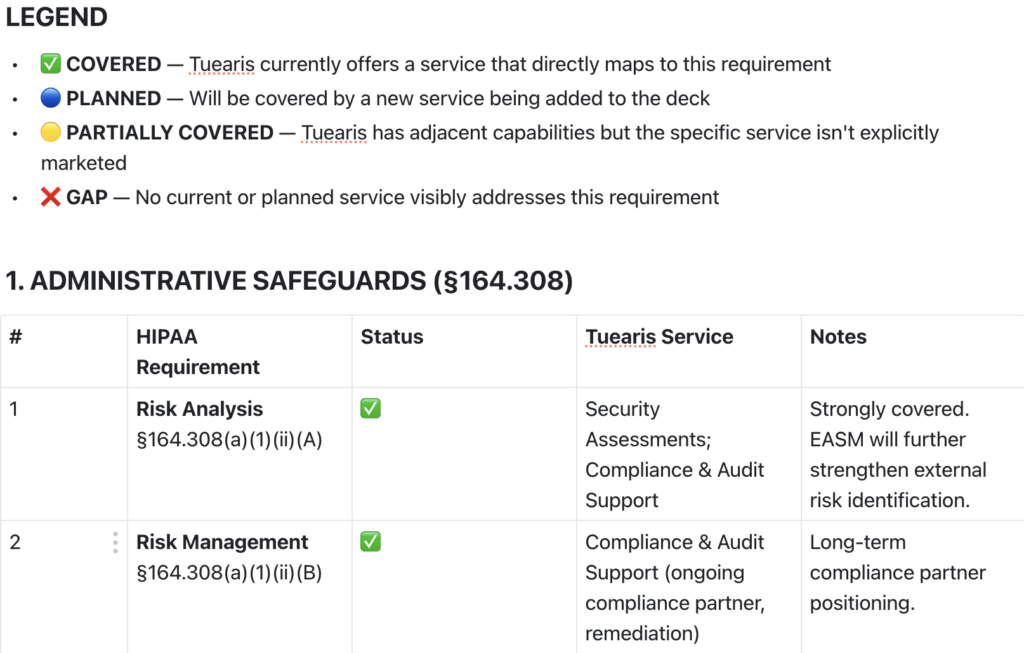
Our Program Roadmap
Our HIPAA Program Roadmap: Every Control We Cover Today and Our Commitments for 2026.
11 years of healthcare security work, documented control by control.
See what our program covers today and every commitment we are building toward in 2026.
Click to explore the full interactive roadmap.
Updated in real time as our program expands. What you see is what is covered today.
MANAGED SERVICES
Cloud Security
Your cloud provider secures the infrastructure. We secure everything built on top of it: your data, your users, and your applications across every cloud platform you operate in.
Extended Detection and Response (XDR)
Unified visibility across endpoints, network, cloud, and identity. XDR connects signals across your entire environment so threats that evade point solutions do not evade us.
Secure Access Service Edge (SASE)
Every user in your organization connects securely regardless of location or device, without the complexity of legacy VPN infrastructure. Zero Trust access controls enforced at the edge across your entire distributed workforce.
Email Security
Phishing detection, anomalous login alerting, MFA enforcement, and outbound content filtering across every inbox in your organization. Email is protected as a clinical communication channel, not treated as an acceptable risk.
Endpoint Detection and Response (EDR)
Continuous behavioral monitoring on every laptop, workstation, and server in your environment. A compromised or stolen device does not become a reportable HIPAA breach.
Managed Detection and Response (MDR)
Automated threat detection paired with continuous analyst monitoring. When a threat is identified in your environment, we respond. Incident response on protected devices is included at no additional cost.
PROFESSIONAL SERVICES


Designed for organizations that need a clear picture of their compliance gaps before committing to a managed program. Our assessments map your current environment against HIPAA's technical safeguard requirements and deliver a prioritized remediation roadmap.


We identify exploitable vulnerabilities before adversaries do. Our penetration testing engagements go beyond automated scanning. We assess your environment using the same techniques a motivated threat actor would apply, targeting the exposures least likely to surface through standard compliance reviews. In one engagement, our team identified unauthenticated access to protected health information during a routine review, before a formal test had even been scoped. The client rebuilt their patient-facing site entirely. No breach notification was required.
Outcome: You understand your actual exposure, not just your reported posture.


HIPAA compliance is an ongoing operational requirement, not a one-time project. We help your organization understand the full scope of its obligations, map existing controls to HIPAA's technical requirements, and prepare for audits with confidence. Our standard program has been validated through a live HITRUST certification audit with zero required modifications.
Outcome: When the auditor arrives, your program is ready.


When an active incident is underway, response time determines outcome. Our incident response team has contained ransomware deployments, stabilized compromised environments, and restored healthcare organizations to operational status under pressure. For existing managed clients, incident response on protected devices is included in your program.
For organizations not currently under a managed agreement: immediate engagement is available. Call 855-580-0055.


Designed for organizations that need a clear picture of their compliance gaps before committing to a managed program. Our assessments map your current environment against HIPAA's technical safeguard requirements and deliver a prioritized remediation roadmap.


We identify exploitable vulnerabilities before adversaries do. Our penetration testing engagements go beyond automated scanning. We assess your environment using the same techniques a motivated threat actor would apply, targeting the exposures least likely to surface through standard compliance reviews. In one engagement, our team identified unauthenticated access to protected health information during a routine review, before a formal test had even been scoped. The client rebuilt their patient-facing site entirely. No breach notification was required.
Outcome: You understand your actual exposure, not just your reported posture.


HIPAA compliance is an ongoing operational requirement, not a one-time project. We help your organization understand the full scope of its obligations, map existing controls to HIPAA's technical requirements, and prepare for audits with confidence. Our standard program has been validated through a live HITRUST certification audit with zero required modifications.
Outcome: When the auditor arrives, your program is ready.


When an active incident is underway, response time determines outcome. Our incident response team has contained ransomware deployments, stabilized compromised environments, and restored healthcare organizations to operational status under pressure. For existing managed clients, incident response on protected devices is included in your program.
For organizations not currently under a managed agreement: immediate engagement is available. Call 855-580-0055.


Management (TVM)
Digital Forensics
Seamlessly Integrated
tuearis cyber
managed servies provider
Built for your stack, not the vendor’s agenda.
tuearis cyber
Protection You
Can Measure



How It Works
From Discovery Call
to Protected PHI.
Here Is What to Expect.

Discovery Call
We learn about your organization, your compliance timeline, and your priorities. If we are the right fit, we will tell you exactly what your program needs and what it will cost.

Architecture and Design
We build your security architecture around your specific technology stack, team size, and HIPAA obligations.

Rapid Deployment
Implementation begins within 10 days of contract execution. Our team is responsive from the moment you sign, even before full deployment is complete.

Monitor, Alert, and Respond
Our team monitors your environment around the clock. When something occurs, your leadership team is notified in near real time, not in a monthly report. Incident response on protected systems is included at no additional cost.

Executive Reporting and Continued Growth
Quarterly reviews keep your leadership informed and confident. As your practice grows, our program scales with you. No disruptions, no PHI risks, no new vendor search.
Proven in Healthcare
We Have Done This Before.
Here Is What That Looks Like

From 20 Employees to 1,500. Zero Service Disruptions
We partnered with one DPC client from their earliest days through HITRUST certification without modifying a single service. When the audit arrived, Tuearis was the only vendor in their entire technology stack that required zero modifications to pass. Their EHR vendor made significant changes to pass. We did not change a thing.

90% Reduction in Critical Vulnerabilities
For the same client, we reduced critical device vulnerabilities from an average of 3 to 4 per device down to 0.3 and sustained that level continuously. That is not a remediation project. That is a managed program

PHI Exposure Identified Before It Became a Breach
During a routine security review, our team identified unauthenticated public access to PHI on a client's patient-facing website. The client rebuilt the site entirely. The incident never required regulatory reporting because we found it first
tuearis cyber
See What People Have To Say About Us

CIO
Manufacturing Company

Business Owner
Medical Services
tuearis cyber
Your Investors Funded a DPC Practice. Make Sure a Breach Does Not Put It All at Risk
There is a narrow window between securing funding and seeing your first patient. It is the most strategic time to build your security program correctly, before there is anything to breach and before there is patient data to protect. Let us show you what that looks like for an organization at your stage
Why Tuearis
We Are Not a Generalist.
Healthcare Cybersecurity Is All We Do
Healthcare-only focus
We specialize exclusively in healthcare cybersecurity. Most vendors are IT generalists with a security practice attached. We have over a decade of healthcare-specific experience. Our distinction is not branding. It is whether your security partner understands how to tune detection tools for a clinical environment, manage a HIPAA incident, and brief your board on risk posture with clarity.
Flat, predictable billing. No exceptions
We do not charge per ticket. We do not bill hourly when your team calls with a question. We do not invoice separately for incident response on protected systems. Your monthly fee is your monthly fee
Direct access to our engineers, not a support queue
From day one, your team communicates directly with the engineers who know your environment. When something happens, you receive a substantive response in real time from the people accountable for your program, not a ticket acknowledgment
Built for where you are today
We handle the complexity so you do not have to. Whether you are starting from zero or inheriting a handful of tools, we build the program your practice actually needs. Our model is fully a la carte, so you are never paying for services your organization does not need